Video Baby Monitor Repair Uncovers Private Data [Hackaday]
As the name of the channel implies, [BuyItFixIt] likes to pick up cheap gadgets that are listed as broken and try to repair them. It’s a pastime we imagine many Hackaday readers can appreciate, because even if you can’t get a particular device working, you’re sure to at least learn something useful along the way.
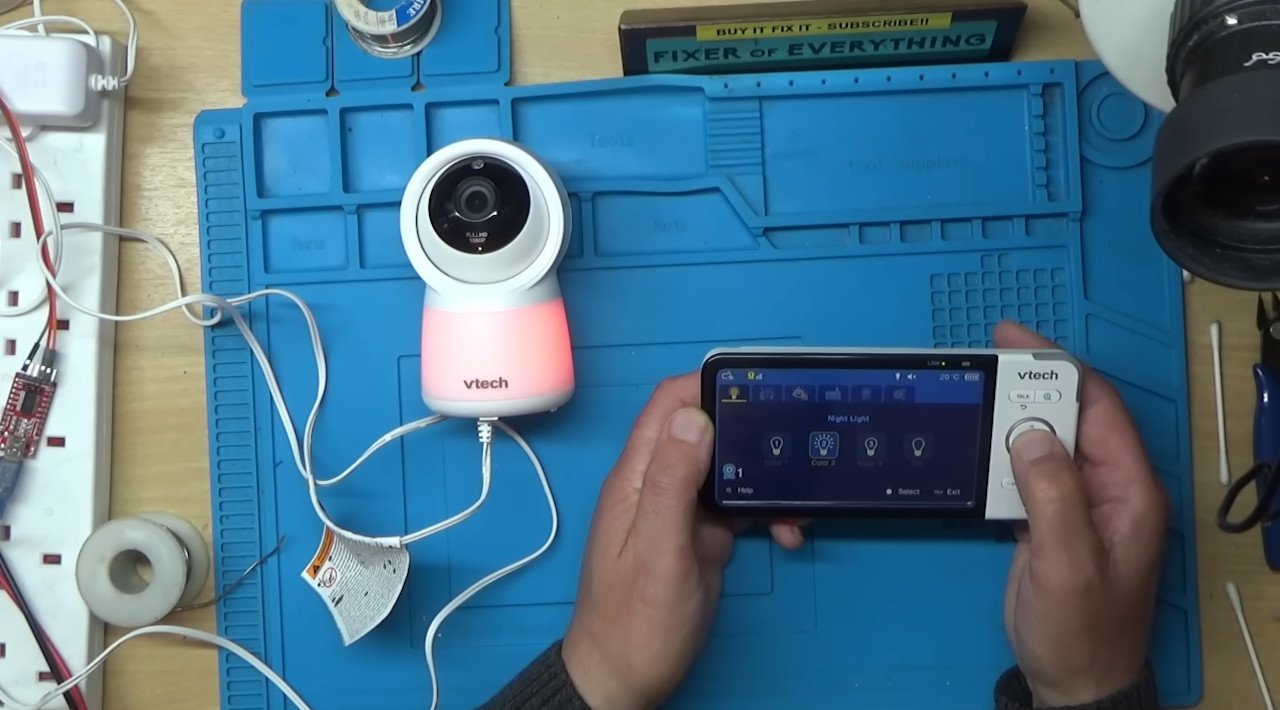
But after recently tackling a VTech video baby monitor from eBay, [BuyItFixIt] manages to do both. He starts by opening up the device and going through some general electronics troubleshooting steps. The basics are very much worth following along with if you’ve ever wondered how to approach a repair when you don’t know what the problem is. He checks voltages, makes sure various components are in spec, determines if the chips are talking to each other with the oscilloscope, and even pulls out the thermal camera to see if anything is heating up. But nothing seems out of the ordinary.
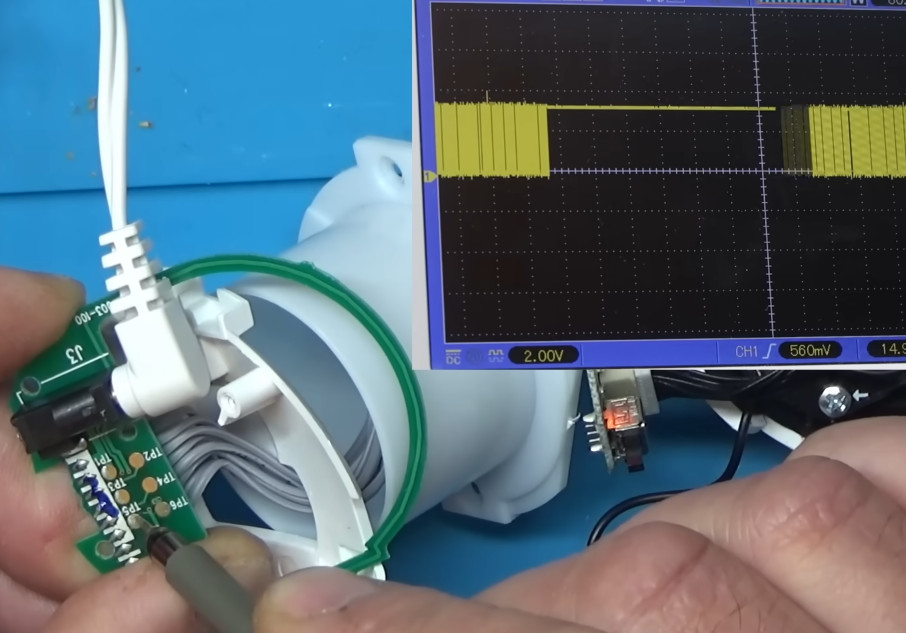
While poking around with the oscilloscope, however, he did notice what looked like the output of a serial debug port. Sure enough, when connected to a USB serial adapter, the camera’s embedded Linux operating system started dumping status messages into the terminal. But before it got too far along in the boot process, it crashed with a file I/O error — which explains why the hardware all seemed to check out fine.
Now that [BuyItFixIt] knew it was a software issue, he started using the tools built into the camera’s bootloader to explore the contents of the device’s flash chip. He uncovered the usual embedded Linux directories, but when he peeked into one of the partitions labeled Vtech_data2, he got a bit of a shock: the device seemed to be holding dozens of videos. This is particularly surprising considering the camera is designed to stream video to the parent unit, and the fact that it could record video internally was never mentioned in the documentation.
While copying the chip’s contents over serial would have been possible, [BuyItFixIt] instead pulled it out and physically dumped the whole thing with a reader. With a bit of Linux-fu, he’s able to mount the chip dump and confirm that the videos in question are of the previous owner’s infant. Yikes. Of course, he promptly deleted the files once he realized what the camera had stored, but it makes us wonder how many cameras like these are holding private video files waiting for a bad actor to uncover them. This is an important reminder of the inherent dangers of tossing away “broken” smart devices.
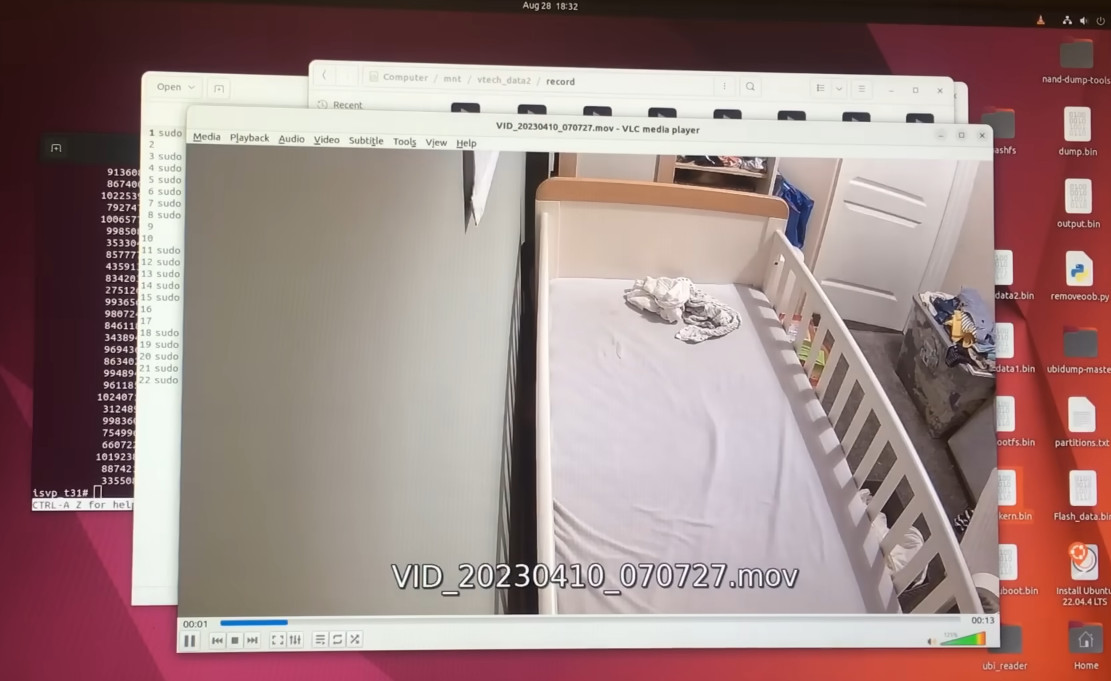
As for the repair itself, [BuyItFixIt] reasoned that some file — maybe the database of videos — must have been corrupted on the chip, so he took the nuclear option and wiped it all out. He had to use the bootloader commands to recreate the partition table, but once that was done, the firmware seemed to understand that it had been returned to a factory state and was finally able to boot up normally. He’s documented the commands he used to get it back up and running in the hopes he can help out somebody else with a similarly ailing camera.
We can never get enough of this sort of firmware hacking, and the fact that this particular bout opened up with a great real-world example of hardware diagnosis makes it all the better. This is a long video, but one that’s well worth your time to check out. If you’d like to see more repairs from [BuyItFixIt], we’ve got you covered.

![video-baby-monitor-repair-uncovers-private-data-[hackaday]](https://i0.wp.com/upmytech.com/wp-content/uploads/2024/09/209734-video-baby-monitor-repair-uncovers-private-data-hackaday.jpg?resize=800%2C445&ssl=1)